Why cloud security?
While the rapid growth of IaaS, PaaS, and SaaS services has helped businesses streamline operations and improve worker productivity, it has also introduced new risks and threats.
Control risky app usage
Improve security configuration
Protect against threats
Integrated DevSecOps
Cloud security solutions
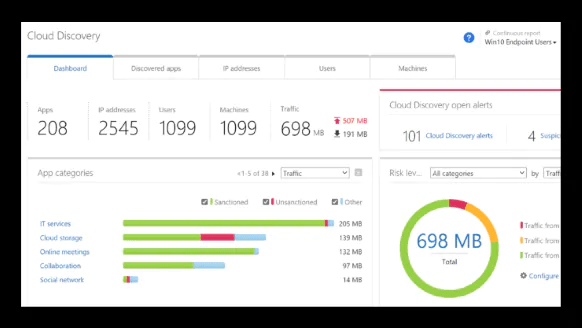
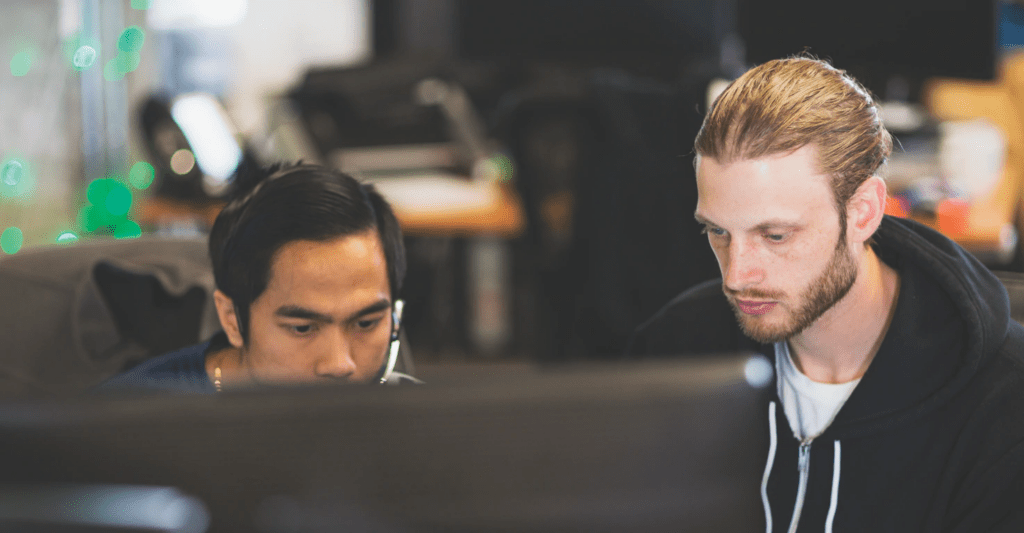
Microsoft Cloud App Security
Get end-to-end protection for all your cloud apps with our leading cloud access security broker (CASB). Designed with security professionals in mind, Microsoft Cloud App Security is built on native integrations, provides customizable automation capabilities, and is optimized for a global workforce.
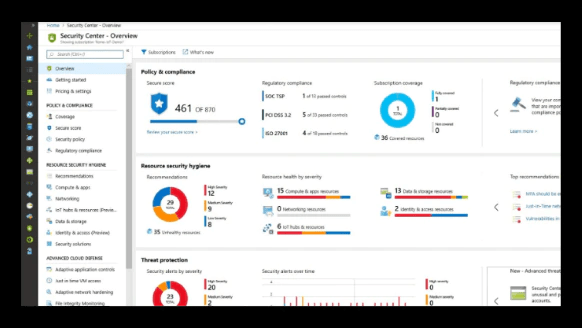
Azure Security Center
Get a comprehensive view of your security posture and Azure environment’s compliance. Monitor and help protect cross-cloud resources and receive best-practice recommendations.
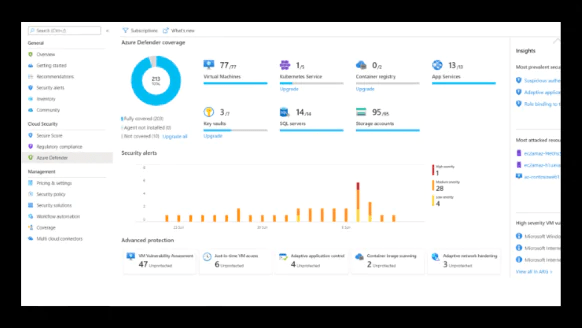
Azure Defender
Use deep-threat intelligence to detect and block malware and threats across servers, data, cloud-native services, and IoT with our cloud workload protection platform.
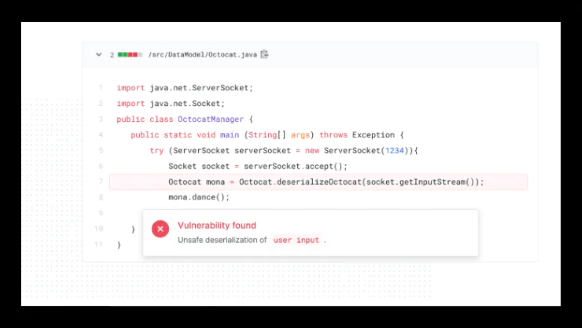
GitHub advanced security
Build more secure apps faster with threat modeling, vulnerability scanning, and unit testing directly inside your release pipeline. Protect your app with encryption and ensure success with our best practices and toolkit.
What is cloud security?
Help protect any app with Microsoft Cloud App Security
Centralize monitoring and control for all apps
Discover and control shadow IT
Identify and remediate cloud-native attacks
Protect your information in real time
Strengthen multicloud security posture with Azure Security Center
Know what’s going on
Get guidance and recommendations
Have more control
Streamline security management
Protect hybrid cloud workloads with Azure Defender
Protect Azure services
Protect hybrid cloud resources
Leverage comprehensive threat intelligence
Develop secure apps with Github
Build secure apps faster
Get dependency updates automatically
Protect the stack, top to bottom
Use our best practices and tools
More on cloud security solutions
Safeguard multicloud apps
What’s new in Azure Security Center
Introducing Azure Defender
What’s new in Microsoft cloud app security
Frequently asked questions
What is Microsoft 365?
How does the data migration process work?
What is the end-user experience like?
The end user can have many benefits like:
- Security: With Microsoft 365, you can use the same systems used by Microsoft and other enterprises worldwide to help protect email, documents, and networks.
- Reliability: With a 99.9% uptime, productivity can be kept at an all-time high which leads to an increase in revenue.
- Compliance: Microsoft keeps all its products and services compliant by all standards.
- Compatibility: Microsoft 365 can be used on all kinds of operating systems be it old or the latest one.
- Up-to-date versions: With Microsoft 365, companies and their users get all the features and functionality of the very latest version of Microsoft’s server products.
- Single sign-on: Users can log into the domain once and are automatically authenticated to Microsoft 365.
- Seamless coordination and collaboration is made easy through Microsoft 365 both inside and outside the organization.
- Anytime, Anywhere Access: Apart from the rich local applications, you can use Web Apps to edit your work even if you are away from your Microsoft365 equipped computer.
- Simple to learn and straightforward to use applications make user experience richer.
With these state-of-the-art but easy-to-use collaboration, mail, and messaging services, you can set yourself apart from competitors.
How reliable is Microsoft 365?
Is there any downtime while the migration occurs?
If I have one Microsoft 365 Business license, on how many devices can I install Office Apps on?
What is your service fee? Are there different plans?
Can I use my existing email address and domain name?
How long is the migration process?
How do I get support if I run into any problems?
Is internet access required for Microsoft 365?
See what customers are saying about Microsoft 365